How to Ensure Email Signature Compliance for Medical Services
Understand email signature compliance for medical services - credentials, HIPAA disclaimers, department-specific rules, and how to prevent violations at scale
Short answer
What does HIPAA compliance require from medical email signatures?
HIPAA-compliant medical email signatures must include the sender’s full name, professional credentials (MD, RN, NP), job title, organization, and contact details. A HIPAA confidentiality notice is also required.
The U.S. Department of Health and Human Services (HHS) requires “reasonable safeguards” on all email containing Protected Health Information (PHI).
Hipaa Compliance Risk
Stop accepting HIPAA liability from unmanaged medical email signatures
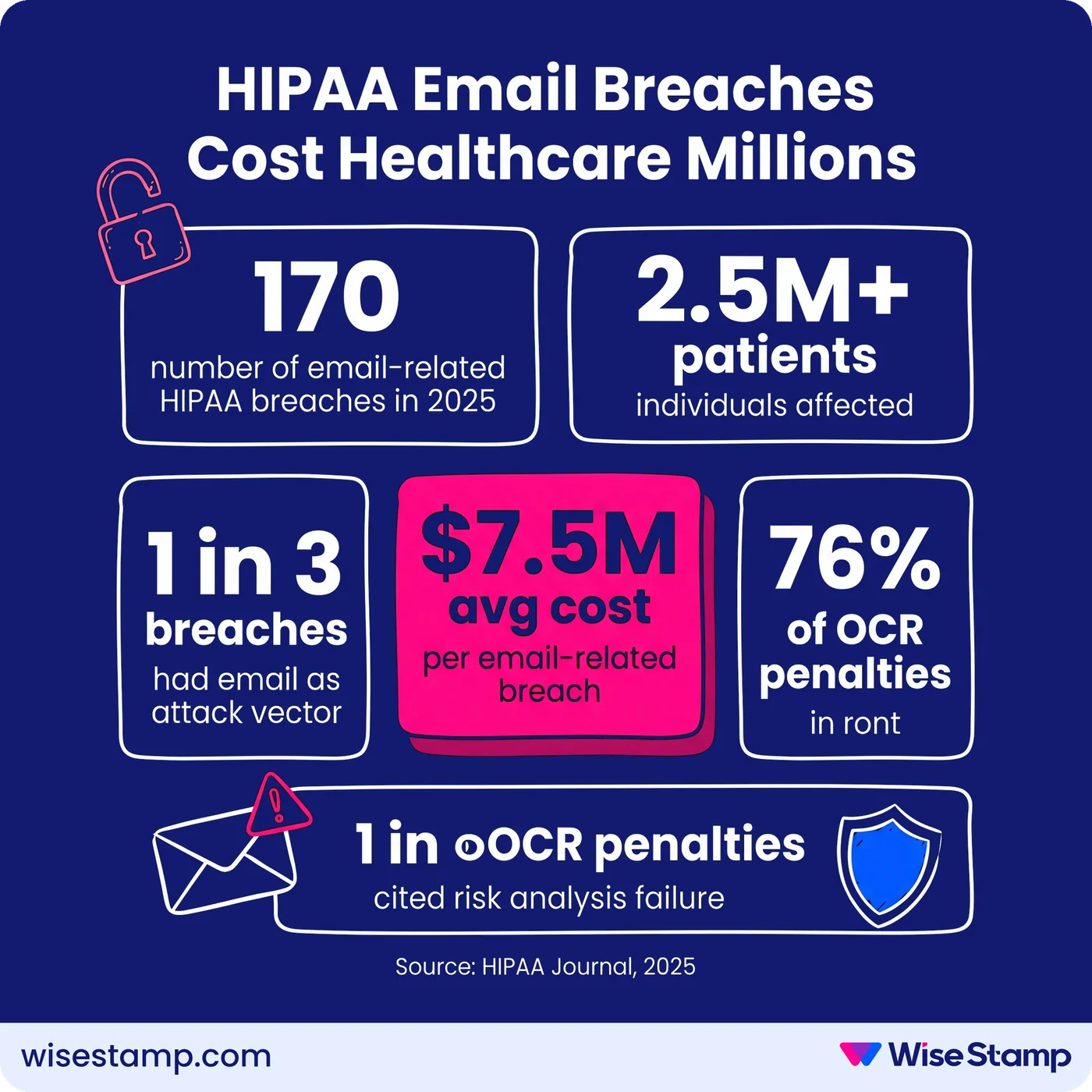
Unmanaged healthcare email signatures are a direct HIPAA enforcement exposure. In 2025, 170 email-related HIPAA breaches affected over 2.5 million people.
Email was the attack vector in 1 in 3 breaches logged on the HHS Office for Civil Rights (OCR) “Wall of Shame” (HIPAA Journal, 2025).
The average cost of an email-related healthcare breach: $7.5 million in penalties and settlements.
Those breaches start small. A new hire emails patients before their signature is configured. An employee changes devices and the disclaimer drops.
A department updates its compliance language but half the team is still running the old footer.
The signature is where email governance either holds or breaks. Without a centralized system, every one of those failure modes runs quietly, at scale, every day.
Hipaa Regulatory Framework
What regulations govern email signature requirements in medical services?
Healthcare email signature compliance sits at the intersection of 2 federal frameworks: the HIPAA Privacy Rule and the HIPAA Security Rule, both codified under 45 CFR Part 164.
The HIPAA Privacy Rule permits covered healthcare providers to communicate electronically with patients.
The standard applied is that they must “apply reasonable safeguards when doing so” (HHS.gov FAQ 570, 45 C.F.R. § 164.530(c)).
The Privacy Rule does not prohibit unencrypted email for treatment-related communication. But it requires that reasonable precautions be in place.
The HIPAA Security Rule requires administrative, physical, and technical safeguards for any electronic Protected Health Information (ePHI) transmitted by email.
Encryption for ePHI in transit is an “addressable” specification under 45 CFR Part 164, Subpart C.
That means covered entities must assess, document, and implement it unless they can justify an equivalent alternative safeguard.
The HITECH Act (2009) extended these requirements to business associates. Any email service provider or signature platform that routes or handles ePHI must have a signed Business Associate Agreement (BAA).
That includes Google Workspace, Microsoft 365, and any third-party platform involved in email delivery.
State medical boards add a further layer. Several states impose stricter requirements on electronic patient communications, credential display, and confidentiality language.
Consult your state’s medical board for jurisdiction-specific obligations that may exceed federal minimums.
Required Signature Elements
What must a compliant medical email signature include?
Medical email signatures serve 2 distinct functions: they identify the sender as a licensed, accountable professional, and they satisfy minimum regulatory disclosure obligations.
A compliant medical email signature must include:
- Full legal name with all active professional credentials (MD, DO, RN, NP, PA, DNP, PharmD, LCSW, APRN, etc.)
- Job title and specialty (for example, “Attending Physician, Cardiology” or “Nurse Practitioner, Family Medicine”)
- Organization name and department
- Direct contact information: office phone number and practice address
- HIPAA confidentiality notice (see the section below for required language components)
One rule that cannot be overstated: email signatures must never contain PHI. Including a patient name, case reference, diagnosis, or treatment detail in a standard signature block is a direct HIPAA violation.
The signature identifies the sender. It carries no patient-specific information.
Credentials must also reflect current licensure. An expired designation or missing specialty creates both a regulatory gap and a patient-trust issue.
In healthcare organizations with high staff turnover or frequent role changes, keeping credentials current manually is where compliance quietly breaks down.
Hipaa Disclaimer Standards
What should a HIPAA email signature disclaimer say?
HIPAA email disclaimers are not legally mandated by the Privacy Rule or the Security Rule. HHS has not issued a regulation requiring a specific confidentiality footer in outgoing email.
That said, they are standard compliance practice across healthcare, widely recommended by healthcare attorneys, and included in most enterprise compliance programs as a best-effort safeguard.
A compliant HIPAA disclaimer includes 4 components:
- Confidentiality statement: the email may contain PHI intended only for the named recipient
- Restriction notice: unauthorized use, disclosure, or distribution is prohibited
- Misdirection instruction: notify the sender immediately if the email was received in error
- Deletion request: permanently destroy all copies if the email reached the wrong recipient
A widely adopted example:
CONFIDENTHALITY NOTICE: This email and any attachments are intended solely for the named recipient and may contain protected health information (PHI) under the Health Insurance Portability and Accountability Act (HIPAA). Unauthorized use, disclosure, or distribution is prohibited. If you received this message in error, please notify the sender immediately and permanently delete all copies.
One important clarification: a disclaimer does not create HIPAA compliance. According to HHS, a confidentiality notice does not protect a covered entity from liability if PHI reaches the wrong recipient.
It signals intent. The actual safeguards are encryption, access control, and email governance architecture.
The disclaimer belongs in the signature. It is not a substitute for the rest of the compliance program.
Role-Specific Requirements
How do healthcare email signature compliance requirements differ by role?
Healthcare email signatures are not uniform. Regulatory obligations vary by role, department, and the type of patient information each staff member handles in the course of their work.
Clinical staff — physicians, nurses, therapists, pharmacists — must display active, current credentials.
A missing licensure suffix or outdated specialty reflects poorly in both OCR audits and patient-facing communications.
Billing and payment-collection roles face additional obligations.
I’ve seen this described by a compliance officer at a large regulated organization:
“From a compliance standpoint too – titles, roles, that kind of stuff. We do have people internally who collect payments, and we need to make sure that compliance-wise, we’re checking all the boxes signature-wise.”
That distinction matters operationally. Billing staff carry different compliance obligations than clinical staff, and their signatures need to reflect those obligations separately.
Shared inboxes — billing@, referrals@, support@ — need their own governed signature configuration.
A generic disclaimer with no identified sender creates an accountability gap in OCR investigations and adds ambiguity to patient communication records.
Why Compliance Fails At Scale
Why do healthcare organizations fail to maintain email signature compliance?
Healthcare email signature compliance breaks down the same way it does in any large organization.
The problem is governed by a policy document, not by enforcement technology.
A compliance team issues a template. IT distributes it by email. Staff copy and paste. Some don’t.
New hires begin emailing patients before their signature is configured. Credentials change after a promotion and no one updates the template. Staff switch to mobile devices and the footer disappears.
An IT professional in a community forum described this directly: “With hundreds of users, you simply cannot rely on people to keep their own signatures updated and consistent.”
This is not a people problem. It is an architecture problem.
In 2025, 76% of all OCR enforcement actions included a penalty for risk analysis failure (HIPAA Journal, 2025 Healthcare Data Breach Report).
A risk analysis that does not address email communication governance, including signature compliance, does not hold up under audit.
Enforcement Architecture
How do healthcare IT teams enforce email signature compliance across all devices?
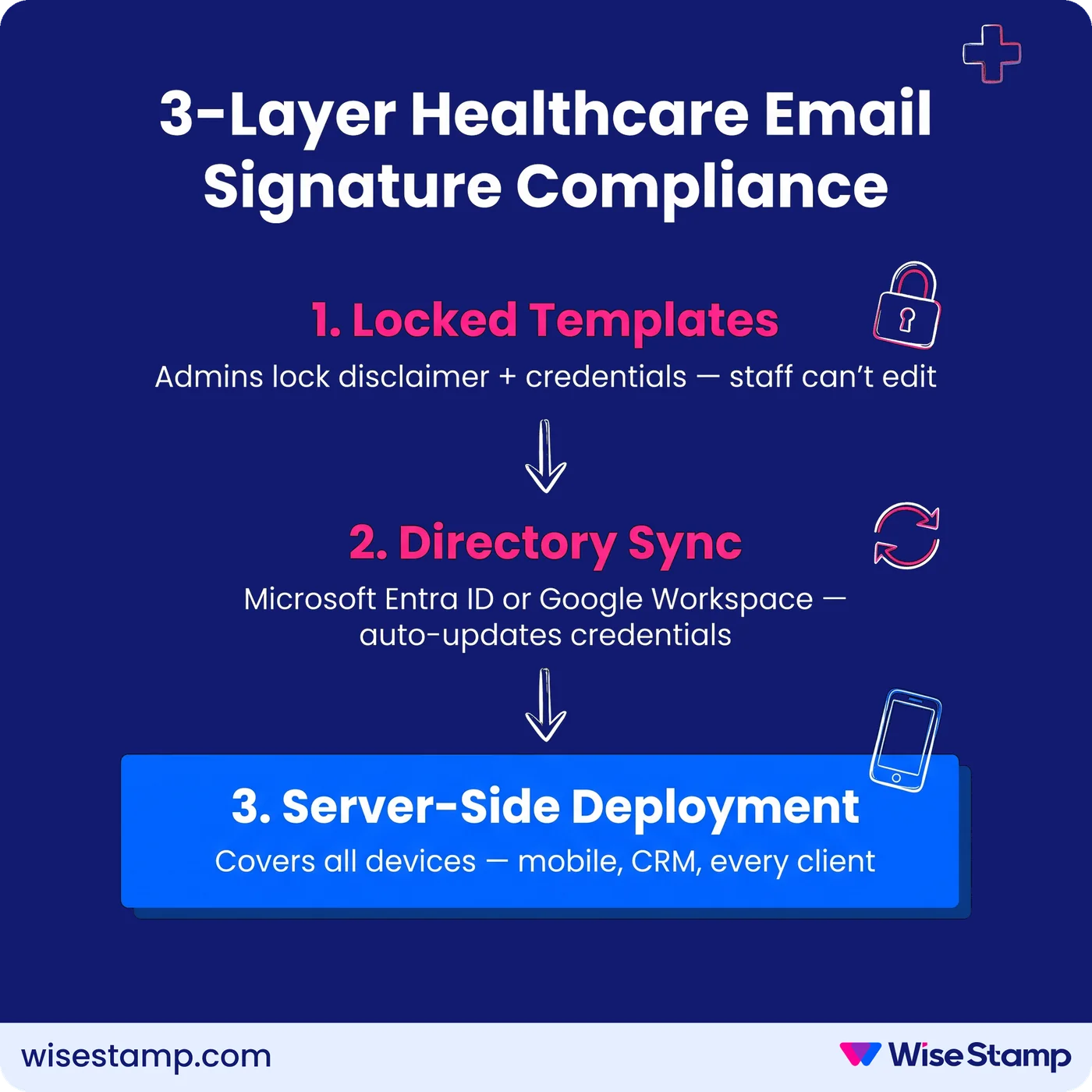
Healthcare compliance requires centralized enforcement, not voluntary consistency. The architecture that holds under OCR audit has 3 components.
Centralized templates with locked fields. One master template per role or department, deployed through Google Workspace or Microsoft 365.
The HIPAA disclaimer, credential fields, and organization details are administrator-locked and cannot be edited or removed by staff. This removes the human error variable from disclaimer compliance.
Directory sync for real-time credential accuracy. Credentials, titles, and department assignments change.
A signature platform connected to Microsoft Entra ID or Google Workspace directory updates signature data automatically on a daily sync.
New hires receive a compliant, current signature from their first outgoing email. Role changes propagate immediately. Departing staff are removed without manual cleanup.
Server-side deployment for complete device coverage. Mobile devices are where healthcare email compliance most commonly fails.
Staff email from personal iPhones. Automated messages leave CRM platforms without any signature attached.
A server-side deployment appends the correct signature to every outgoing message at the mail server level, regardless of device, client, or application.
This closes the mobile and CRM coverage gap that client-side solutions leave open.
WiseStamp supports all 3 layers in a single platform. Admins lock compliance fields and connect to Google Workspace or Microsoft Entra ID for daily directory sync.
Hybrid deployment is also configurable for full coverage across every device and email client.
WiseStamp is HIPAA-compliant, SOC 2 Type II certified, and ISO 27001 and ISO 27018 certified, which satisfies the security review requirements common in healthcare procurement.
Department-specific groups let clinical, billing, and administrative staff carry different governed templates from one admin interface.
When disclaimer language needs to change because of a policy update or new regulatory guidance, it is updated once and reflected across the organization instantly.
Takeaway
What does sustainable email signature compliance in healthcare actually require?
Sustainable healthcare email signature compliance is not achievable with distributed templates and voluntary adoption. It requires centralized enforcement applied to the signature layer with the same rigor applied to any other regulated patient communication channel.
The 3 requirements that hold up under OCR audit:
- Locked templates by role: clinical, administrative, and billing staff carry different governed signature content, with compliance elements immutable at the employee level
- Automated provisioning: new hires receive compliant signatures through directory sync on day one; departing staff are removed automatically
- Universal device coverage: server-side deployment ensures every outgoing email, from every device and client, carries the current, correct signature
With 170 email-related HIPAA breaches in 2025 and OCR enforcement intensifying, email signature governance is no longer a nice-to-have in healthcare organizations. It is part of the risk analysis.
See how WiseStamp supports healthcare email compliance requirements
Takeaway
Key Points
Medical email signature compliance requires adherence to the HIPAA Privacy Rule, Security Rule (45 CFR Part 164), and the HITECH Act (2009).
Applicable state medical board regulations add a further jurisdiction-specific layer.
Required signature elements include full name, professional credentials, job title, organization, contact details, and a HIPAA confidentiality notice.
Disclaimers are strongly recommended but not mandated by HHS under either the Privacy or Security Rules (HHS.gov FAQ 570).
In 2025, 170 email-related HIPAA breaches affected over 2.5 million people, with an average enforcement cost of $7.5 million per breach (HIPAA Journal, 2025).
Compliant signature governance requires centralized templates with locked fields, directory sync from Microsoft Entra ID or Google Workspace, and server-side deployment for complete device coverage.